Overview
When using a Cisco ASA with the AnyConnect VPN Client software in some instances it is useful to assign the same static IP address to a client whenever they connect to the VPN. Within Active Directory you can configure per user a static IP address and use this IP address whenever the user connects to the VPN. The RADIUS Server (in this instance Cisco ISE 2.0) can be configured to query the attribute in AD which is the” msRADIUSFramedIPAddress” value and assign to the client whenever they connect.
This post only describes configuring a static IP address on a Cisco AnyConnect Remote Access VPN. Refer to the following posts for more detail instructions on how to configure ASA Remote Access VPN and integrated with Cisco ISE for authentication:
ASA AnyConnect SSL-VPN
ASA AnyConnect IKEv2/IPSec VPN
Software/Hardware Used:
Windows 7 SP1 (Client)
Windows 2008 R2 (Active Directory Domain Controller)
Cisco ISE 2.0 (RADIUS Server)
Cisco ASAv v9.6(1)
Cisco AnyConnect Client 4.2.01022
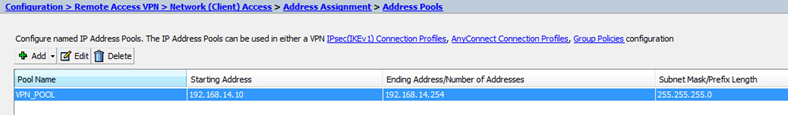
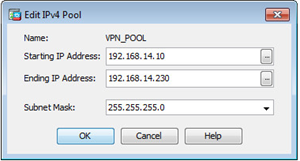
Cisco ASA Configuration
- Modify the existing IP Address Pool to decrease the number of IP addresses, leaving space at the end of the range (or beginning) to be used for statically assigned IP addresses.
AD Account Modification
- Select a test account within AD
- Modify the properties of the test account; select the “Dial-in” tab
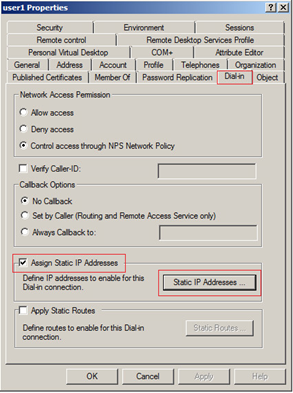
- Tick the “Assign Static IP Address” box
- Click the “Static IP Address” button
- Tick “Assign a static IPv4 address” box and enter and IP address from within the IP address range defined on the Cisco ASA appliances
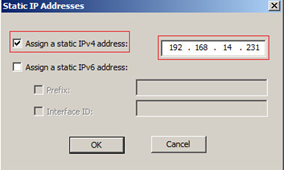
- Click “OK” to complete the configuration
Cisco ISE Configuration
Add AD Attribute
- Modify the configuration of the existing Active Directory External Identity Source and select Edit
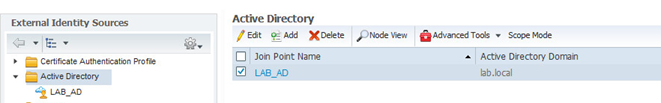
- Click “Attributes” tab
- Click “Add” > “Select Attributes from Directory”
- Enter the name of the test user previously modified to add the Static IP address and select “Retrieve Attributes”

- Ensure you tick the box “msRADIUSFramedIPAddress” and click “Ok”
IMPORTANT – If you do not previously assign as static IP address to the user account you are using to query AD for the list of attributes the “msRADIUSFramedIPAddress” will not be in the list to select.
- Edit the attribute “msRADIUSFramedIPAddress” and change the “Type” value from STRING to IPv4
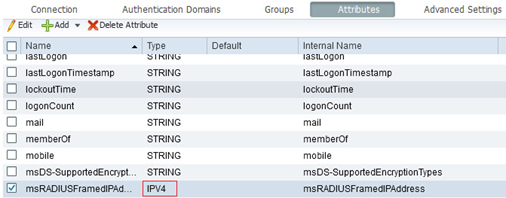
- Click “Save”
Create Authorization Profile
- Create a new “Authorization Profile” called “Static-VPN-IP-Address” – Policy > Policy Elements > Results > Authorization > Authorization Profiles
- In the Advanced Attributes Settings add a new value for “Radius:Framed-IP-Address” and equals the “msRADIUSFramedIPAddress” value previously added
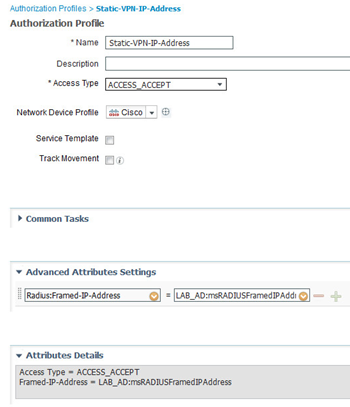
NOTE – “LAB_AD” will equal the name of YOUR Active Directory
Modify Policy Set
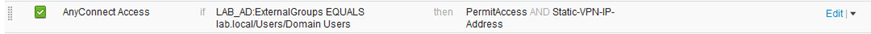
- Modify the existing Policy and the “Static-VPN-IP-Address” Authorization Profile
Test AnyConnect VPN Client
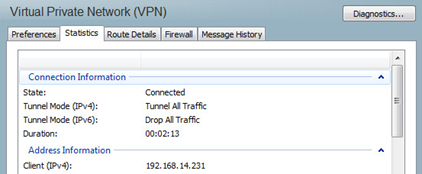
- Log in to the VPN using the test client, once successfully authenticated you can check to see if the client has been assigned the correct IP address
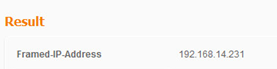
- Within the RADIUS authentication logs double check to confirm the Framed-IP-Address value was used
Repeating the test for a user that does NOT have a static IP address assigned with in AD continues to work and an IP address is assigned from configured IP Address Pool on the ASA.
2 thoughts on “ASA AnyConnect VPN with Static Client IP Address”